USBsamurai For Dummies. How to Make an USB Malicious Implant &… | by Luca Bongiorni | InfoSec Write-ups

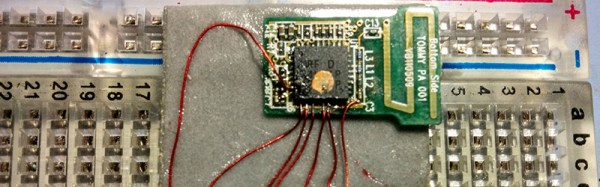
How to Inject Keystrokes into Logitech Keyboards with an nRF24LU1+ Transceiver « Null Byte :: WonderHowTo

Matt Perks Creates First USB Type-C Logitech Unifying Receiver Dongle in History — and Shows You How - Hackster.io
![photos] I got my split wireless build to run off a logitech unifying receiver. : MechanicalKeyboards - MECHKEYS photos] I got my split wireless build to run off a logitech unifying receiver. : MechanicalKeyboards - MECHKEYS](http://i.imgur.com/Ivra7nB.jpg)
photos] I got my split wireless build to run off a logitech unifying receiver. : MechanicalKeyboards - MECHKEYS


/cdn.vox-cdn.com/uploads/chorus_asset/file/19165619/Screen_Shot_2019_09_03_at_8.52.08_PM.png)








:max_bytes(150000):strip_icc()/LogitechUpdatingTool-4768666-8f5df6ea8972474ba6490617e1e56d6d.jpg)

/cdn.vox-cdn.com/uploads/chorus_image/image/64725036/logitech-cube-mouse-review-main-1024.0.jpg)
/Logitech-mouse-4768666-882b1106dd7746108837c9bf6b8efec7.jpg)



